
Bio
A computer science and IT enthusiast in the fields of international relations. Exploring the interesting interaction between cyberspace and international relations. His research spans cyberspace, cyber-politics and recent developments in ICT. He focuses on questions such as: How and to what extent the cyberspace has changed the IR(if any)? Is there a global hegemony in cyberspace? Will there be power transition in cyberspace?
Cyberspace is evolving in an unimaginable pace and it is bringing inevitable changes the way human, states and organizations of all kind interact.
Academic Positions
Education & Training
-
Ph.D.(on going) 2018-
Ph.D. in IR (candidate)
Yıldırım Beyazıt University, Ankara
-
P.G2012
Post-Graduate Study in Strategic Military Planning
Joint War College, Istanbul
-
M.A2004
Master of Arts in International Security
Army War College, Istanbul
-
M.S2000
Master of Science in Computer Science
Naval Postgraduate School, Monterey,CA
-
B.A.1993
Bachelor of Science in Electric-Electronics
National Defense University, Ankara
Research Summary
As part of the global commons, cyberspace is fundamentally changing our way of production, life and thinking. As civilization develops, cyberspace has already become an integral part of society, the study of which is of far-reaching significance.
Cyber warfare, meaning interstate cyber aggression, is an increasingly important emerging phenomenon in international relations, with state orchestrated (or apparently state- orchestrated) computer network attacks occurring in Estonia (2007), Georgia (2008), Iran (2010), USA(2016) and apparently Russia, China and Israel as well.
Some researchers point that ‘low-level’ and isolated nature of cyber-attacks do not fit the notion of ‘war’ as commonly understood. In this sense, the term ‘cyber warfare’ is adapted in my research. It is not necessarily used to denote scale or protraction, or even ‘violence’ per se, in the sense of a ‘war’ as it is perhaps generally understood. Thus, the term ‘cyber warfare’ is employed broadly to convey an interstate element in the use of technological force in cyberspace: that is, ‘the realm of computer networks (and the users behind them) in which information is stored, shared and communicated online’.
This method of waging warfare – given its potential to, for example, make planes fall from the sky or cause nuclear power plants to melt down – has the capacity to be as devastating as any conventional means of conducting armed conflict. it should always be kept in mind that just because the existing examples of what my research is terming ‘cyber warfare’ have been relatively isolated and small-scale does not necessarily mean that future attacks of this sort will be. Indeed, the examples of cyber aggression that have occurred in practice show a notable progression of scale. Because almost every state in the world now has a cyber- defence programme and over half of the states also have a cyber- attack programme adding to the complexity of the cyberspace.
Contrary to the views of a minority of commentators who have downplayed the threat posed by interstate cyber-attacks, my research closes to the point that cyber warfare is an emerging phenomenon in international relations, with state-orchestrated (or apparently state-orchestrated) computer network attacks against other states occurring with increasing frequency and scale. This increasing activity also might be sign of power transition in cyberspace with all references to increasing debates about rise of China.
Interests
- Cyber politics
- Cyber conflict
- Software Development
- BlockChain
- Artificial Intelligence
- IoT
- Robotics
- Machine Learning
- Cyber Security
Research Projects
-
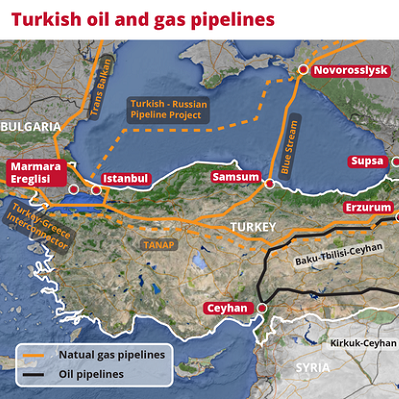
Geopolitics has become the key challenge in access to energy supplies globally. According to the BP Statistical Review of World Energy, much of the world’s oil and gas reserves are located in certain parts of the world: the Middle East, North Africa, the Caucasus, and the Commonwealth of Independent States (CIS) account for nearly 80 percent. If we look at countries in specific detail, six countries produce half of the world’s oil, and three countries produce half of the world’s gas.
On the other hand, the countries that consume these reserves are much more diversified. The supply of energy is critical for OECD countries in Europe and the Pacific region. The trading of energy supplies has become much greater in terms of volume and more global in its scope. The world’s geopolitical situation has brought out a greater need for interdependence and cooperation between producer countries and consumer countries. As we all know from current events, accidents, military conflicts, and terrorist attacks cause problems for the supply and transport of hydrocarbons, especially in critical transit points. Thus, energy security has become an important priority for many countries, since it is seen as vital for economies.
Turkey’s demand for energy is increasing in line with its economic growth. Her fundamental need is to secure reliable energy to fuel its economic development But, as a result of its geopolitical environment, the country faces many important challenges and opportunities.
-

Digital transformation is not just about modernizing technology and tools. It is about adopting appropriate digital technologies to change how we work, deliver public value, and build prosperity through the emerging digital economy. Blockchain, also known as a distributed ledger technology, stores different transactions/operations in a chain of blocks in a distributed manner without needing a trusted third-party. Blockchain is proven to be immutable, which helps with integrity and accountability, and, to some extent, confidentiality through a pair of public and private keys. Blockchain has been in the spotlight after successful boom of the Bitcoin.
Blockchain functions as a shared digital ledger running on multiple computers in a public or private network. Blockchain software aggregates transaction records into batches or “blocks” of data, links and time-stamps the blocks into chains that no one can change or delete without the consent of a majority of participants; instead, shared governance protocols verify and record data automatically. As a result, blockchain provides an immutable, transparent record of transactions. Some researchers call it the Internet of value because we can use it to store, manage, and exchange anything of value—money, securities, intellectual property, deeds and contracts, music, votes, and our personal data—in a secure, private, and peer-to-peer (P2P) manner. We achieve trust not necessarily through intermediaries like banks, stock exchanges, or credit card companies but through cryptography, mass collaboration, and some clever code.
Use cases tend to focus on financial services. Government agencies could also use blockchain not just for conducting financial transactions and collecting taxes, but also for registering voters, identifying recipients of healthcare, financial support, and emergency aid; issuing passports and visas; registering patents and trademarks; recording marriage, birth, and death certificates; and maintaining the integrity of government records. Blockchain offers good solution for many applications that need transparency, decentralization, integrity, immutability, and security without requiring trusted third party. However, there are several challenges to be addressed to realize the full potential of blockchain for different applications and use cases. Typical challenges to be addressed include the following. • Throughput and bandwidth in the blockchain network: Is existing network bandwidth enough for blockchain transactions and updates to do real-time updates in the systems? We need to more research to address this challenge. • Latency/delay in blockchain network: How often the ledger should be updated in the blockchain and what is the least tolerable updating delay that is acceptable? Furthermore, adversary can disallow a miner’s block from reaching all other miners for a long time. How can we address these types of attacks more effectively? • Energy consumption in blockchain: What could be the minimum/optimal energy consumption for such computationally complex operations in blockchain?
In many ways, Blockchain today is comparable to where the Internet was in early 1990s. While we have witnessed how the ‘Internet of Information’ has changed our societies over the past two decades, we are now entering a phase where Blockchain is likely to do the same by ushering ina new paradigmcomprising ‘Internet of Trust’ and ‘Internet of Value’. It is expected to disrupt the way stakeholders would interact in a decentralized framework of trust, thereby increasingly democratizing value. Banks and financial services institutions play a very important role in those wider societal interactions today and Blockchain is therefore forcing them to rethink their roles to stay relevant in this emerging paradigm. It's early days, but industry leadersare sponsoring a wide range of blockchain use cases supported by industry consortiums. Having seen the potential of this technology and the challenges, we think the opportunity is clear but the blue sky is too far off and companies need to validate use cases and business / technical viability before implementing blockchain.
-

To be detailed.
Publications
Filter by type:
Sort by year:
An ad hoc wireless mobile communicationsmodel for Special Operations Forces
Master of Science Thesis Naval PostGraduate School, Monterey, CA, Sept 2000
Abstract
The digitization of the battlefield enables special operators to use improved communications supported by computer networks across a range of missions. The communications paradigm is evolving toward mobile wireless ad hoc networks. This development enables an autonomous system of mobile nodes supporting peer-to-peer communications in forward-deployed military networks. Ad hoc networks have to establish a reliable, secure, instant, and usually temporary, communication infrastructure and to be able to access in a global communications infrastructure. Our model describes a global communication network supporting the special operator in mobile wireless communications. The main purpose is to provide a handheld wireless communications node which is capable of transferring voice, data, and imagery to and from parallel and vertical command structures within an environment replete with electronic countermeasures. The model will support the representation of requirements such as throughput, quality of service with low power consumption, and low probability of detection/interception. Special Forces are moving toward using commercial-off-the- shelf products and services based on availability and cost effectiveness. Using GloMoSim tool, we run simulations for a direct action scenario and compared the efficiency of on-demand and table-driven routing protocols under different bandwidths and communications loads.
The Dragonfly Effect: Quick, Effective, and Powerful Ways To Use Social Media to Drive Social Change
Book John Wiley & Sons | September 28, 2010 | ISBN-10: 0470614153

Proven strategies for harnessing the power of social media to drive social change
Many books teach the mechanics of using Facebook, Twitter, and YouTube to compete in business. But no book addresses how to harness the incredible power of social media to make a difference. Lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
Lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco laboris nisi ut aliquip ex ea commodo consequat. Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
- Lorem ipsum dolor sit amet, consectetur adipisicing elit.
- Lorem ipsum dolor sit amet, consectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
- .sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
- Onsectetur adipisicing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua.
Teaching
Cyber-Politics Classes to be planned...
Currrent Teaching
Teaching History
At My Office
Please contact me at your convenience...
At My Work
Please contact me at your convenience...
At My Lab
Please contact me at your convenience...